Learn about email security including identifying fraudulent emails, email encryption, and more.
How to Identify Fraudulent Emails
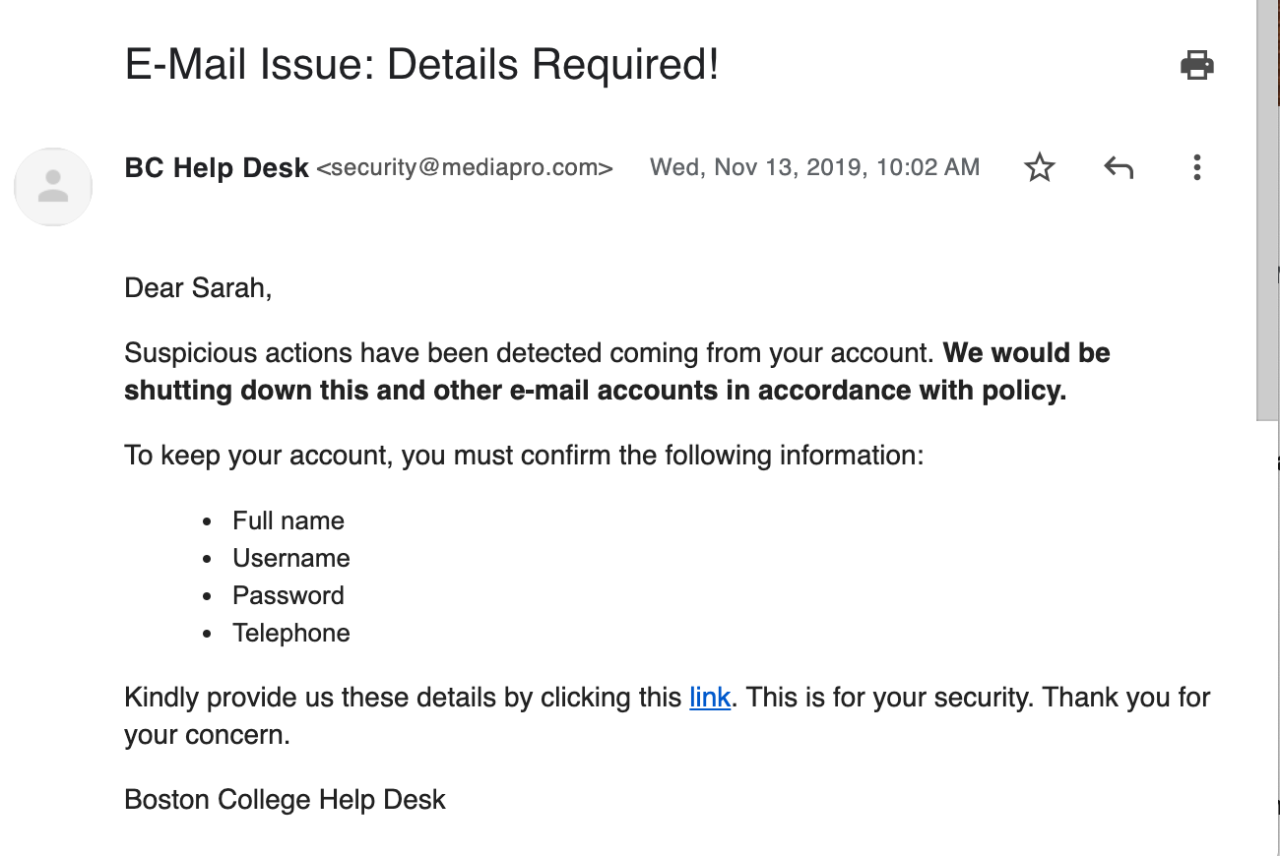
Cyber criminals use compelling email messages to trick you into clicking a link, downloading an attachment, or replying to an email. Once you have reacted to their message, they steal sensitive information or install malicious software on your computer.
When interacting with email, do not rely on any single approach to identifying a scam, know all the possible signs (especially #4):
An urgent subject line, language prompting you to act quickly.
A direct email you were not expecting (even if it appears to be from someone you know, or someone at BC).
- Be aware, occasionally a legitimate BC email account is hacked, and used to send scam emails to other BC community members.
“From” addresses with sneaky variations of (legitimate) email addresses. Examples: Ending in @bc-edu.org instead of @bc.edu
- Get in the habit of checking the from/signed by. See below for details.
- Messages from a BC person or department that do not have an @bc.edu in the email address should be viewed with extreme skepticism.
- A sender name is easy to fake.
- If you aren’t sure if an email is authentic, instead of replying, contact the sender using information you already have about them (such as their BC email address from the BC Directory).
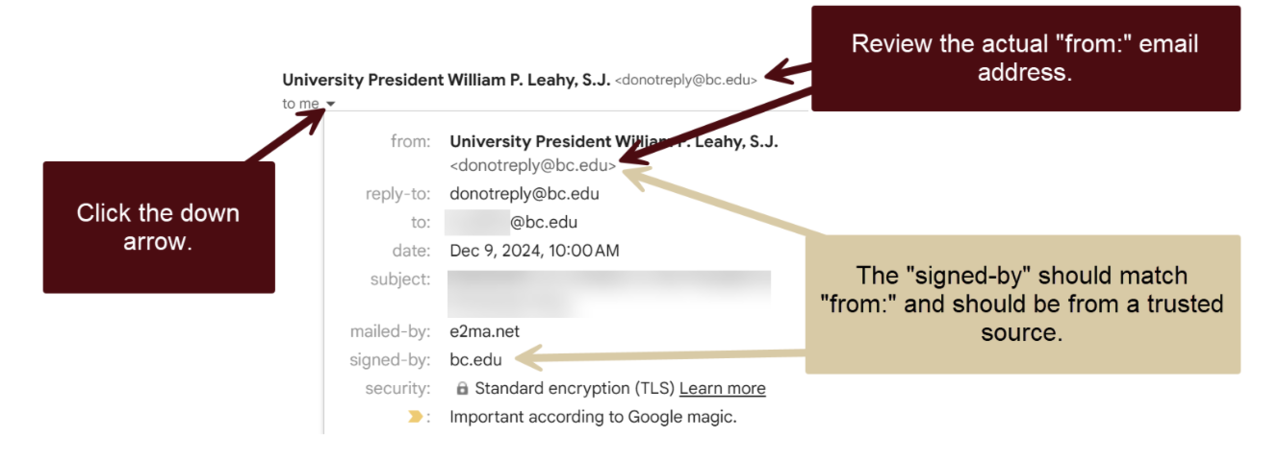
How to Verify the Sender Email Address in Gmail
- Next to the Sender Name, click the down arrow to view more sender information.
- Review the actual From Email Address located inside the angled brackets.
- Example: BC Help Center <help.center@bc.edu>
- Review the “signed-by:” and verify the domain it was sent from is what you’d expect. It should match the portion of the email address that follows the “@” in the From Email Address.
What about hacked accounts? Beware. If someone's email account has been compromised, it may be used to send malicious emails. So even if a sender email address appears authentic, always be cautious if an email has any of the other warning signs that it could be a scam.
- Never click on an attachment you were not expecting. You could unknowingly download a virus or ransomware to your device.
- Just because it looks like a BC sign in page doesn’t mean it is!
- Any link that takes you to a form that looks like the BC sign in page BUT has a non-BC web address, is a SCAM.
- BC will NEVER ask for a password unless it is on an official BC login screen. Official login screens always have bc.edu before the first single, forward slash (/), for example:
https://login.bc.edu/nidp/idff/sso?id=19&sid=0&option=credential&sid=0
- Just because it looks like a Google sign in page, doesn’t mean it is!
- Scammers also create log in pages that look like Google log in screens, but aren’t! Instead they are just hoping to steal your credentials and access your Google account.
- Official Google log in screens always have google.com before the first single, forward slash (/), for example:
https://accounts.google.com/v3/signin/identifier?authuser
=0&continue=https%3A%2F%2Fmail.google.com%2Fmail&ec
=GAlAFw&hl=en&service=mail&flowName=GlifWebSignIn&flowEntry
=AddSession&dsh=S606954128%3A1728478423789165&ddm=1
https://docs.google.com/document/d/1uIGZq3yh5sE_d9N-fA4GOZKO5zxrwMGaEKyUHtcA4hY/edit
- Hovering over a link to see the web address can helpful. However, many departments on campus use third party email marketing tools to send messages, which can cause a link to a legitimate web page to look like “https://t.e2ma.net/click/p0obxi/lt0szkrb/haz7hu”. In those cases, when it doubt, go to www.bc.edu website and search for the information mentioned in the email.
Typos, odd phrasing, unnecessary capital letters are often indicators of a scam.
Official BC emails will not have QR codes in the body.
What to do if you receive a fraudulent email
- Do not reply to the email, or text/call any phone numbers included in the email.
- Do not click on any links or attachments in the message.
- Forward the original email message* to: phishing@bc.edu
You will receive an AI-designed follow-up email letting you know if the email was malicious, safe, spam, or phishing simulation. As AI is an experimental tool, you may occasionally receive an incorrect assessment.
- If possible, in Gmail, click the three dots in the upper right corner and select, “Report phishing” or “Report spam.”
* What not to forward to phishing@bc.edu
In order for the email security tool to give you an assessment:
- Do not forward screen shots of emails or text messages
- Do not forward emails with additional text
- Do not forward emails that weren’t received by you directly
Avoid Your Spam and Trash Folder
Messages in Spam and Trash folders were automatically moved out of your Inbox because they were identified as spam or phishing. They may contain malicious emails, so please avoid reading or interacting with messages in these folders. Only check Spam and Trash if you're expecting a message that hasn’t arrived in your Inbox. There is no need to report messages found in these folders to phishing@bc.edu.
Think You've Been Compromised?
Report a Security Incident
If you think you’ve been the victim of a phishing email, email security@bc.edu to report it. A member of the IT Security team will follow-up with you.
Protect Your Account
- Change your BC Password and BC Gmail Passwords. Phishing emails often target your credentials so they can access your email account, or your BC account, and gain access to your private data. Change your passwords, and take away their access.
- Change other passwords. If you use your BC passwords on any other accounts, change those passwords as well.
- Log out of all other Gmail Sessions. If a bad guy got a hold of your BC Gmail login, they may be logged into your account. Kick them out! In the bottom right corner of Gmail, click Details and then Sign out all other web sessions.
- Check your Sent Mail folder. Bad guys often use compromised email accounts to send malicious messages to others in your contacts. If you see emails were sent from your account which you did not send, this would confirm your account has been compromised, and will let you know who has received an email from your account.
- Check your mail forwarding settings. Bad guys often enable mail forwarding, so messages sent to your email will be forwarded to an account of their preference. Disable unwanted email forwarding by going to Settings > Forwarding and POP/IMAP > Disable forwarding > Save.
- Check your Google email settings and remove any suspicious accounts. Go to Settings > Accounts > Send Mail As.
- Report the email as phishing in Gmail. Learn how to report an email as phishing in Gmail.
- Scan your computer for malware or viruses.
Email Security
Electronic Abuse
While Boston College strives to provide an open computing environment to foster collaboration and learning, there are policies defining appropriate use of the BC network and computing resources, such as email. Before reporting electronic abuse, make sure you are familiar with BC's computing policies and guidelines.
Examples of Electronic Abuse and Appropriate Action to Take
- Your system/server has been or is being attacked: Report the abuse immediately and do not make any changes to the system until you hear from the ITS security team on campus. You may accidentally remove vital information that can be used as evidence.
- You received offensive or threatening email or voicemail: Do not delete the offensive message as it can be used as evidence.
- You suspect someone knows or is using your BC password: Report the compromise immediately with any substantiating evidence. Change your password immediately.
- You are aware of software copyright violations at Boston College.
Report Electronic Abuse
Send an email to abuse@bc.edu describing the electronic abuse. You must show the full message headers of any email message that you are forwarding. Do not delete the email from your inbox until you have heard back from us.
Encrypted Email with Virtru
If you need to send confidential emails as part of your job, you may want to consider requesting Virtru. Virtru is an email security tool that allows you to:
- encrypt emails
- prevent a forwarded encrypted email from being read
- set a read expiration date on encrypted messages
- and revoke the ability to read an email after it is sent
Getting Started with Virtru
If you think you may need this service, contact your Technology Consultant. Once approved, install Virtru for Gmail or Outlook.
Email recipients do not need to install Virtru to read or respond to your email. Recipients of an encrypted email will not be able to access the message directly from their inbox. Rather, they will be prompted to "unlock" the message, and verify their email address.
ITS recommends you inform your recipients to expect an encrypted email, since they will be prompted to take extra steps to unlock the message. The best way to do this is to add a customized intro to your message. Be sure to include information that only your recipient would know, or write it in such a way that they know it's really you.
By default, all Vitru encrypted messages will be automatically decrypted. You can install the Chrome plug-in, which will allow you to respond to any Virtru messages sent to you. However, you will not be able to initiate a Virtru encrypted email with the free version of Virtru.
Email Security Service
BC employs an email security service integrated with BC's Gmail to safeguard against malicious emails. This AI-powered service automatically detects and eliminates threats like phishing, malware attachments, and business email compromises. Additionally, it complements Gmail's existing spam filtering to further minimize the number of harmful emails reaching your BC inbox.
What to Expect
Although this service will reduce the number of email threats, it is still imperative to be mindful when you receive suspicious emails.
- Emails identified as significant threats are automatically moved to a secure, hidden location that is inaccessible to you. This "invisible" layer of defense prevents accidental clicks on dangerous content.
- Think an email has been hidden by mistake? If you suspect a legitimate email has been hidden from your inbox in error, please contact the Help Center at 617-552-HELP (4357) or help.center@bc.edu, or your local Technology Consultant, so ITS staff can restore it to your inbox.
- Any other suspicious emails that are not deemed to be significant threats are automatically moved to your BC Gmail Spam folder.
- Report Suspicious Emails. If you receive an email that looks suspicious, forward it immediately to phishing@bc.edu. You will receive an AI-generated reply letting you know if the email was malicious or safe. As AI is an experimental tool, you may occasionally receive an incorrect assessment.
Questions?
Contact the BC Technology Help Center for assistance at help.center@bc.edu or (617) 552-HELP (4357).
Boston College implemented a Phishing Simulation program to increase awareness and education related to phishing emails, therefore decreasing the risk of exposure of University data. Phishing simulation is ongoing for all students and for select faculty and staff, by department request.
Why is BC Doing This?
Colleges and universities continue to report increased phishing incidents in which bad actors try to trick people into clicking on malicious links in an effort to steal passwords, access personal or University data, and in some cases encrypt data and demand money for the data to be unencrypted.
Sample Phishing Simulation Educational Web Page
If you mistakenly click on a phishing simulation email link or attachment, you will be taken to a web page that explains which characteristics of the email were clues of a typical scam.
Sample Phishing Simulation Email